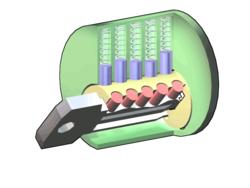
To those who retain faith in mechanical pin and tumbler locks, a bit of information on the bump key as a means of picking them may unsettle you. It’s a hot topic on many of the news aggregation sites online at the moment (Metafilter and Engadget 1 and 2, for instance), but those who don’t frequent such sites may find it helpful to know. Perhaps the biggest issue is that this technique does not produce signs of forced entry, which may cause problems when making insurance claims.
This Dutch television segment shows how absurdly easy it is to open even quite expensive locks using a key cut in a particular way, an object to whack it with, and no skill whatsoever. Definitely enough to make a person fearful for their laptop, music equipment, etc. That is especially true in an area that has as high a burglary rate as North Oxford. Just last night, Emily saw someone trying to get into her flat. Thankfully, the front door of our flat uses horizontally-oriented “dimple” keys (Mul-T-Lock brand), that are somewhat less vulnerable to this attack (see the last PDF linked at the bottom of this post). Even so, our internal doors, as well as basically all the ones in Wadham College, use the pin and tumbler design vulnerable to bumping. Here is another video on how to make and use a bump-key. Apparantly, anyone with a file, a reasonably steady hand, and a bit of time can make their own.
The alternatives generally advanced to get around such vulnerabilities are other sorts of mechanical locks, electronic access control systems, or systems that use both mechanical and electronic elements (a system used increasingly often in cars). While they do have problems of their own, electronic access control systems do have many appealing features. In particular, if one were to use low-cost RFID tags or simple swipe-cards with a pre-set code as an authentication token, it would be easy to maintain a database of allowed and disallowed keys. If you lost your keys, you could disable that one and issue yourself a new one. Likewise, temporary keys could be issued to people, and restrictions could be placed upon the hours at which certain keys could be used. Features like these are what make keycard based systems so appealing, as well as common in commercial settings.
The first downside of such conversion is cost: replacing locks is expensive. Secondly, such systems are open to other kinds of attacks that people may not understand as easily. Thirdly, if an electronic lock fails in a profound way (no longer responds to authentication tokens), you have little choice but to break down the door or saw through the frame and bolt. Once again, the nature of security as a perpetual trade-off is demonstrated.
More detailed information (PDF) on key bumping is available from Security.org. Also, from The Open Organization of Lockpickers (TOOOL) (PDF).

“Lockpicking information until very recently has been hidden not from the bad guys, but from us, the consumers,” says security guru and author Bruce Schneier, a cryptographer with enough clout to get a little shout out in Dan Brown’s “The Da Vinci Code.” “There’s no economic motivator for anyone to make a better lock because you, the consumer, don’t know [how vulnerable your lock really is].”
There are ways to improve upon locks, says Schneier. He points to the auto industry, which has an incentive to build cars that are tougher to break into. “If your car is easier to steal, your insurance will be more [expensive],” he points out. So automakers have begun equipping cars with locks that open only with the swipe of a card or in close proximity to a radio frequency identification (RFID) chip.
From a Newsweek article (heavily laden with ads, sorry)
R.K.
I agree with you 50%. What’s going to protect you while you are sleeping with your alarm deactivated? Nothing. Bumpkeys can open 80-90% of houses in the US.
And heck, with sites like http://www.bumpkey.us out there getting bump keys is a little too easy.
If you want the best protection start with a lock that can’t be opened in 10 seconds by a retarded 2nd graded.
HackVI,
I would say that dual-factor authentication (physical key and RFID) is the best option: at least for those with enough of a technical bent to have the interest and ability to handle a key database.
For others, it seems best to spread the word about serious vulnerabilities in mechanical locks until manufacturers and users have enough motivation to at least switch to more effective mechanical solutions.
The gardens at Wadham College, at least, are secured using a warded lock. So too, the rooms in Library Court.
An archaic type of lock, it’s generally trivial to circumvent, given a few basic tools and some knowledge.
“A Warded pick is a device for opening warded locks. It is a pick generally made using a key-shaped piece of thick spring steel (two hacksaw blades thick) and with the sides being as thin as possible without breaking off in the lock.
Such a pick will open nearly all warded locks on garden sheds, garages, etc.
Note: These are what people are referring to when they speak of skeleton keys. They are usually available in sets of five for about $20. They can easily be made by taking a key that comes with a warded lock and filing or grinding away all the protrusions except one or two at the end. These will work on many but not all warded locks.”
Bruce Schneier also wrote about this vulnerability, linking the TOOOL paper.
Defence in depth is a very basic security measure. Having an imperfect light, along with other measures such as automatic exterior lighting, good insurance, and other defenses might be better than just having a better lock.
HackVI
My point was more than we need to focus on complete security systems than just on the level of security provided by a particular barrier. That said, the level of threat associated with bumping (especially given the insurance issue) might be serious enough to compromise an entire setup.
This is even worse:
How to open a Mazda using a tennis ball
Snopes.com now has an article on bump keys.
“I apologize to
you. At the end of this presentation you will not feel comfortable
anymore, realizing the trust you put in mechanical locks in the past
was based on wrong assumptions. For real security the mechanical lock
is a lost battle …”
From a presentation to the German Navy.
Another mechanical lock vulnerability:
HOWTO force a padlock with a tin-can shim
This short video illustrates a simple procedure for forcing open standard padlocks with a shim snipped out of a tin can. The technique is old, but this is a good, lucid explanation of it. Kids have been doing this for years, but schools and gyms still recommend these broken locks — and the manufacturers keep making them, which is practically criminal negligence.
See also: HOWTO pop a combination lock with a beer can
Golden (bump proof) pins
May 12th, 2008 by Barry
Pick a Lock, Any Lock
YouTube makes it easy to learn the finer points of breaking and entering—and locksmiths aren’t happy.
By Farhad Manjoo
Posted Wednesday, July 23, 2008, at 3:39 PM ET
Locksmiths and lock manufactures have found themselves in a jam. The skills of their trade, passed down through generations under conditions of occult secrecy, have been jimmied open online (subscription required). The professionals are crying foul over enthusiasts of “locksport”—amateur lock pickers who congregate on the Web to discuss how to pick locks. The amateurs do this for fun, not mischief, they say; there’s a sublime thrill in charming a deadbolt to turn your way. And they argue that by finding and publishing flaws in some of the most popular locks on the market—from the locks you’ve got on your front door to those the president has on his—they’re forcing improvements in security. Lock professionals say the opposite is true: that in showing people how to pick locks, hobbyists are swinging your doors wide open to criminals.
TENNIS BALL DOOR UNLOCKER – Trying to use a tennis ball with a hole cut in it to unlock a car door does not work. There is no part of the unlocking mechanism that can be affected by the small amount of air from the tennis ball. This myth was recently busted on the show. They also tried a strong, air compressor as well. Still could not unlock the car door.
The Ultimate Lock Picker Hacks Pentagon, Beats Corporate Security for Fun and Profit
By Charles Graeber 05.22.09
The Ultimate Explorer’s Tool
6 gauge copper wire is perfect for this problem for two reasons. Number 1, it is stiff enough to maintain a shape once bent despite a reasonable amount of pressure applied to it. Number 2, it is bendy enough that you don’t ruin your soft typing fingers on it. 4 gauge: too hard. 8 gauge: too soft. 6 gauge: just right.
I bought 13 feet, but you really only need 8 or so. I cut a strip just using a pair of wire cutters. Bend your wire into this shape:
The importance of this shape is that the wire will appropriately slip under the door when laid flat, flip up when turned with the back handle, and lean against the door so it slides between the handle and the door on the other side.
The RFID Hacking Underground
They can steal your smartcard, lift your passport, jack your car, even clone the chip in your arm. And you won’t feel a thing. 5 tales from the RFID-hacking underground.
By Annalee Newitz
James Van Bokkelen is about to be robbed. A wealthy software entrepreneur, Van Bokkelen will be the latest victim of some punk with a laptop. But this won’t be an email scam or bank account hack. A skinny 23-year-old named Jonathan Westhues plans to use a cheap, homemade USB device to swipe the office key out of Van Bokkelen’s back pocket.
“I just need to bump into James and get my hand within a few inches of him,” Westhues says. We’re shivering in the early spring air outside the offices of Sandstorm, the Internet security company Van Bokkelen runs north of Boston. As Van Bokkelen approaches from the parking lot, Westhues brushes past him. A coil of copper wire flashes briefly in Westhues’ palm, then disappears.
Van Bokkelen enters the building, and Westhues returns to me. “Let’s see if I’ve got his keys,” he says, meaning the signal from Van Bokkelen’s smartcard badge. The card contains an RFID sensor chip, which emits a short burst of radio waves when activated by the reader next to Sandstorm’s door. If the signal translates into an authorized ID number, the door unlocks.
The coil in Westhues’ hand is the antenna for the wallet-sized device he calls a cloner, which is currently shoved up his sleeve. The cloner can elicit, record, and mimic signals from smartcard RFID chips. Westhues takes out the device and, using a USB cable, connects it to his laptop and downloads the data from Van Bokkelen’s card for processing. Then, satisfied that he has retrieved the code, Westhues switches the cloner from Record mode to Emit. We head to the locked door.
Ten Things Everyone Should Know about Lockpicking & Physical Security
Deviant Ollam
Open Sesame: Access Control Hack Unlocks Doors
By Kim Zetter
August 4, 2007
Zac Franken, a DefCon goon (staffer), gave a brilliant presentation at the DefCon hacker conference today involving security access control systems and cards for building entrances that use electromagnetic coupling.
The hack involves exploiting a serious vulnerability inherent in the Wiegand protocol that allows an intruder to trick the system into granting entrance to a building to an unauthorized visitor, to lock out authorized visitors and to collect authorization data about everyone who has entered that door to gain access to other areas in a building secured with Wiegand-based readers.
The Wiegand protocol is a plain-text protocol and is employed in systems that secure not only some office buildings but also some airports. Franken has said that it’s used at Heathrow airport. Retina scanners, proximity scanners and other access systems all use the Wiegand protocol so the vulnerability isn’t device-specific.
Rights Amplification: Reverse-Engineering Master Keys
Clearly, the most valuable, sensitive secret in any lock system is the bitting of the top-level master key (TMK). Insiders, who possess legitimate change keys and have physical access to locks, represent perhaps the most serious potential threat against master keyed systems. The primary purpose of assigning locks unique change key bittings, after all, is to allow operating privileges to be granted to only specific locks; if a change key can be converted into a master key, a major security objective of the system is compromised. In the terminology of computer security, master key systems should resist unauthorized rights amplification (also called privilege escalation). Unfortunately, most deployed master key systems are quite vulnerable in this regard.
“We tested our attack against a variety of medium- and large- scale institutional master keyed installations, including both educational and commercial environments. Systems tested were both relatively new and relatively old, had been both factory-keyed as well as privately rekeyed, and included locks manufactured by Arrow (SFIC), Best (SFIC), Corbin Russwin, Schlage, and Yale. For the Best SFIC, Arrow SFIC and Schlage systems, we used portable key punches and a supply of blank keys brought to the facilities tested. For the Corbin Russwin and Yale systems, we pre-cut six test keys on a general purpose code machine (based on measurements previously taken from a change key) and used a metal file at the test site to progressively cut the test keys and finally to cut the full master bitting onto a fresh blank key.
…
In every case, the attack yielded the top master key bitting, as expected. In general, it required only a few minutes to carry out, even when using a file to cut the keys. All six Arrow SFIC and Best SFIC systems we tested had all (six or seven) pin stacks mastered with a TPP format. The two Corbin Russwin (system 70) systems each had three pin stacks (out of six) mastered, again with a TPP format. The Schlage system used an RC-based scheme, with every pin mastered and two master cuts used on each change key. The Yale system was also RC-based, with one master cut used on each change key. Several of the systems had multi-level mastering hierarchies; the attack yielded the TMK in all cases.”
Guide to Lock Picking
Ted the Tool
September 1, 1991
The big secret of lock picking is that it’s easy. Anyone can learn how to pick locks.
The theory of lock picking is the theory of exploiting mechanical defects. There are a few basic concepts and definitions but the bulk of the material consists of tricks for opening locks with particular defects or characteristics. The organization of this manual reflects this structure. The first few chapters presents the vocabulary and basic information about locks and lock picking. There is no way to learn lock picking without practicing, so one chapter presents a set of carefully chosen exercises that will help you learn the skills of lock picking. The document ends with a catalog of the mechanical traits and defects found in locks and the techniques used to recognize and exploit them. The first appendix describes how to make lock picking tools. The other appendix presents some of the legal issues of lock picking.
CLIQ and other “unpickable” locks pwned at DefCon
By Cory Doctorow on maker
Lockpicking legends Marc Weber Tobias, Toby Bluzmanis and Matt Fiddler demo’ed a series of ingenious hacks for opening “unpickable” locks at Defcon last weekend. Included is a hack that opens the expensive electronic/mechanical CLIQ lock, which requires an electronic handshake between the key and the lock, and which logs every open/shut event) by simply vibrating the key:
Bluzmanis demonstrated an attack by taking an Interactive CLIQ electro-mechanical lock made by Mul-T-Lock and inserting a mechanical-only key cut to the same keyway. After inserting the key, he does something to vibrate the key for a few seconds until the mechanical motor in the cylinder turns and lifts the locking element to release the lock. He asked Threat Level not to disclose the precise method, other than to say it involves no special tool or skill.
“There’s no audit trail that the lock has been opened,” Tobias says, “because there are no electronics [involved].” If the attacker entered the room to steal documents or sabotage the facility, the last person who entered before him and who showed up in the audit log, would presumably get the blame if the thief wasn’t caught on surveillance camera or the video surveillance was also sabotaged.
Lockpicking and the Internet
By Bruce Schneier
Physical locks aren’t very good. They keep the honest out, but any burglar worth his salt can pick the common door lock pretty quickly.
It used to be that most people didn’t know this. Sure, we all watched television criminals and private detectives pick locks with an ease only found on television and thought it realistic, but somehow we still held onto the belief that our own locks kept us safe from intruders.
The Internet changed that.
First was the MIT Guide to Lockpicking, written by the late Bob (“Ted the Tool”) Baldwin. Then came Matt Blaze’s 2003 paper on breaking master key systems. After that, came a flood of lock picking information on the Net: opening a bicycle lock with a Bic pen, key bumping, and more. Many of these techniques were already known in both the criminal and locksmith community. The locksmiths tried to suppress the knowledge, believing their guildlike secrecy was better than openness. But they’ve lost: Never has there been more public information about lock picking — or safecracking, for that matter.
Lock companies have responded with more complicated locks, and more complicated disinformation campaigns.
There seems to be a limit to how secure you can make a wholly mechanical lock, as well as a limit to how large and unwieldy a key the public will accept. As a result, there is increasing interest in other lock technologies.
As a security technologist, I worry that if we don’t fully understand these technologies and the new sorts of vulnerabilities they bring, we may be trading a flawed technology for an even worse one. Electronic locks are vulnerable to attack, often in new and surprising ways.
Let’s keep the discussion about locks and physical security open.
I have been looking forward to the HAR conference for a long time. After all, it was going to be the moment to publicly talk about our discovery on bypassing the electronic locking part on the first generation Mul-T-Lock Cliq. More then one year ago we discovered the samples we had in some instances could be opened with the so called ‘magnetic ring’ (you still needed to have the correct mechanical key or bypass the mechanical part). An important discovery as the attack would not show up in the electronic logfile in the lock. And the integrity of the logfile is a key issue in these kind of systems. So we immediately informed Mul-T-Lock about this problem. And even though communication did not always go smooth we came to an agreement. We agreed to go into full detail about this at the HAR conference in 2009. And that is what we just did. At the presentation we showed the problem was not magnetism … it was vibration!
…
I like to keep things simple. If we discover a vulnerability in a lock we will notify the manufacturer. We will tell them what we know and most of the time an interesting and technical discussion is started. And sometimes the manufacturer is a little reluctant and barely wants (or dares) to communicate. Especially in the US the stakes can be high for them because of the ‘I will sue you’ culture. So in a way we understand both approaches and are fine with them, as long as it is clear we will go public on the vulnerability at one moment in time. In general we are talking giving them three to six months, although a longer period can be negotiated if that time is needed to update specific projects or customers.
The philosophy behind this is approach is to give the manufacturer some time to fix the problem, inform it’s customers, exchange locks or prepare a press statement. The fact they know a publication is coming should be enough to motivate them to do the right thing. Going public on the vulnerability will send out a clear signal: better make good locks! There are motivated people out there paying attention to what you do and who will write about it if weak spots are discovered.
Printing police handcuff keys …
By Barry on SSDeV
German SSDeV member Ray is known all around the world for his impressive collection of handcuffs and his fun ways of opening most of them. On top of that he gives great presentations and always manages to add a lot of humor into them!
a plastic 3D printed key that will open the handcuffs of the Dutch police
At HAR he pulled another stunt: He used a 3D printer to print handcuff keys. And not just any ordinary handcuff key … no, it’s the official handcuff key from the Dutch police! At first the police officers at HAR were a little reluctant to event try out the plastic key he printed. But he found another way to verify the key he printed was the correct one. I guess these officers never thought about wearing keys concealed, especially when talking with Mr. Handcuff himself. Given the megapixel camera’s on the market today it was not so difficult to verify the key he printed was the correct one.
Someone is looking at your butt …
At the end of the day he talked the officers into trying the key on their handcuffs and … it did work! At least the Dutch Police now knows there is a plastic key on the market that will open their handcuffs. A plastic key undetectable by metal detectors….
And Ray made it easy for you. For those of you wanting to print your own Dutch police handcuff key … the STL file is available online at http://ke.y.nu/
*Warning* Before you print out your keys please check your local law! Reading the article below (pdf mirror) should be a fair warning! In some places it is not quite healthy to run around wearing police handcuffs ….
HOWTO reproduce a key from a distant, angled photo
By Cory Doctorow on maker
Sneakey is a project from Benjamin Laxton, Kai Wang, and Stefan Savage at the UCSD vision lab that has shown that it is possible to duplicate keys from photos taken at a distance and/or an angle. They’ve published a paper and are offering to release their code if there is “sufficient interest.”
http://blackbag.nl/?p=1122
Advanced foil impressioning
By Barry on foil picking
In 2002 I already demonstrated the theory behind the ‘foil impressioning‘ method at the H2K2 conference in New York. The foil impressioning method is nice because it will open quite a number of high security locks and requires relatively little skill to do so. The only thing you need to have is a key cut to the deepest position (preferably a little deeper) and some adhesive aluminum tape that is used in the automotive and heating industry. You apply the adhesive tape over the holes of the key, trim the edges a bit and insert it into the lock. All you need to do now is put some turning pressure on the key and make small ‘up and down’ movements. The pins that are not in the correct position will bind and become stuck in the lock. These pins will push the tape in a little when the key is pushed upwards, and in the next round of ‘turning and rocking the key up and down’ these binding pins will keep pushing in the tape deeper and deeper until sheer line is reached. The interesting thing is that once a pin reaches the ’sheer line’ (opening position), it is no longer stuck and will not push in the tape deeper. The key will fit itself…
It is a great technique that is around for quite some time. In my collection of picktools I have some impressioning kits made for the locksmith market in 1995 and 1996. These kits use either foil or candle wax to keep the pins in place. If you take a close look on this key for example, you can see they milled a small fraction of the thickness of the key to make room for the foil. The key including the foil will push all pins to the highest position (or so we hope).
There are no secrets in locksmithing, just skill,information,technology and work.work.work. I am a locksmith under the age of 45 and most of the other lock smiths I know over this age still today think there are (secrets). GET OVER IT! If you are one of them. Lockmithing is not beyond rocket science. Thank You to all who post on the net of any type of information that can be used to better others.
XKCD: Unpickable
“At the Defcon security conference in Las Vegas, Marc Weber Tobias and Toby Bluzmanis plan to demonstrate simple hardware hacks that expose critical security problems in Swiss lock firm Kaba’s E-plex 5800 and its older 5000. Kaba markets the 5800 lock, which Bluzmmanis says can cost as much as $1,300, as the first to integrate code-based access controls with a new Department of Homeland Security standard that goes into effect next year and requires identifying credentials be used in secure facilities to control access. One attack uses a mallet to ‘rap’ open the lock, another opens the lock by putting a pin through the LED display light to ground a contact on the circuit board, and a third uses a wire inserted in the lock’s back panel to hit a switch that resets its software.”
Ottawa Police warns residents of a rash of Break and Enters
(Ottawa) – Over the past month, the Ottawa Police Break & Enter Team has noticed a trend of break-ins to residential apartment buildings throughout the City of Ottawa. The suspects appear to be gaining entry into the units by using a “Bump key” method. This consists of a shaved down key being inserted into the lock and defeating the locking mechanism. Unlike picking the locks, which often renders the lock inoperable, the bump key unlocks the door and does not damage the lock.
In some instances, tenants of these buildings have had suspicious individuals knocking on their doors and when answered the individuals deliver a fake story. The suspects are taking items that can easily be carried away, such as laptops, jewelry and cash.
High Security Handcuffs Opened With 3D-Printed and Laser-Cut Keys
Unlock your doors with an iPhone
Nice attempt to fix picking and bump keys:
https://youtu.be/1MnZM8Pkvmw
Now It’s Easier than Ever to Steal Someone’s Keys
The website key.me will make a duplicate key from a digital photo.
—
KeyMe is a secure and convenient way to copy, share and personalize keys. We also help solve frustrating lockouts. Get the App, or visit a Kiosk today!
I’ll Let Myself In: Tactics of Physical Pen Testers
Copying a Key by Listening to It in Action
Phone app can figure out the shape of your house key by listening to you use it
Acoustic cryptanalysis the a kind of security attack made possible by analyzing the sounds of a computer or other device, like reconstructing printouts from the noise of print heads or determining what someone is typing based on the click of each keystroke. Now, National University of Singapore researchers have applied acoustic cryptanalysis to house keys, demonstrating that it’s possible (although difficult) to figure out the most likely shapes of a key by analyzing the sounds it makes in the lock. From their research paper, titled “Listen to Your Key: Towards Acoustics-based Physical Key Inference“