Perhaps it would be wise to interrupt regular blogging, while my thesis is coming together. Upon reflection, however, I find that the issue is more that I am not using time efficiently, and less that important tasks are absorbing too much of it. As ‘a’ (and probably ‘the’) major conduit between myself and most of those who are important to me, internet based communication does not seem unimportant. The task, then, is to pare away activities that do not contribute to the completion of this task (itself unlikely to be relevant in five or ten years) and focus upon those that advance towards the goal.
Category: Writing
Anything on the process or results of writing as an activity and a passion
Filling the gaps in chapter two
The conclusion from working on my second chapter is that I have read too much general background material and not enough on my case studies. I am fairly well covered on POPs, since I have done research on them before. Naturally, adding a few more sources would be nice, though there are not really a great many out there. I am also quite well covered on current events relating to climate change, because there has been such a raft of coverage and discussion. While my intention has never been to write a blow-by-blow account of either (how could I possibly do so in 30,000 words?), it is certainly necessary to have a comprehensive understanding of the history, before any important and valid analysis can be done.
As such, I need to fill in my knowledge on recent developments pertaining to POPs, which should not be hugely difficult. Then, I need to shore up my section on the early history of the climate change debate. Aside from the mandatory OUSSG dinner and talk tonight, I suspect this will fill the next 32 hours. Naturally, I am interpreting my promise to Dr. Hurrell of having a second chapter dropped off at Nuffield by Wednesday as having that chapter dropped off, by my own hand, in time for him to read it on Thursday morning.
Policy{hyphen, space, nothing}making
One minor hiccough regarding the thesis has been cropping up continuously of late. One of my key terms has a trio of possible forms, each of which has a certain appeal and a certain problem:
- Policy making
- Policy-making
- Policymaking
I think all three are acceptable English, and my preference vacillates between the three based on the context in which the word is used. When it is being used as the subject of a sentence, the two word version seems more natural: “Consideration of framing issues is important for those involved in policy making.” When it is modifying a noun, either the conglomerated or hyphenated version seems better: “The policymaking process is fraught with uncertainties.”
I should, however, choose a single form to use in the entire thesis, and do so before I need to wade through too many tens of thousands of words and footnotes to set the standard. Preferences, anyone?
I am working on developing presentation standards for the whole thesis. I am told Oxford has some rules of its own, but I am not sure where to find them.
Making a hash of things
The following is the article I submitted as part of my application for the Richard Casement internship at The Economist. My hope was to demonstrate an ability to deal with a very technical subject in a comprehensible way. This post will be automatically published once the contest has closed in all time zones.
Cryptography
Making a hash of things
Oxford
A contest to replace a workhorse of computer security is announced
While Julius Caesar hoped to prevent the hostile interception of his orders through the use of a simple cipher, modern cryptography has far more applications. One of the key drivers behind that versatility is an important but little-known tool called a hash function. These consist of algorithms that take a particular collection of data and generate a smaller ‘fingerprint’ from it. That can later be used to verify the integrity of the data in question, which could be anything from a password to digital photographs collected at a crime scene. Hash functions are used to protect against accidental changes to data, such as those caused by file corruption, as well as intentional efforts at fraud. Cryptographer and security expert Bruce Schneier calls hash functions “the workhorse of cryptography” and explains that: “Every time you do something with security on the internet, a hash function is involved somewhere.” As techniques for digital manipulation become more accessible and sophisticated, the importance of such verification tools becomes greater. At the same time, the emergence of a significant threat to the most commonly used hashing algorithm in existence has prompted a search for a more secure replacement.
Hash functions modify data in ways subject to two conditions: that it be impossible to work backward from the transformed or ‘hashed’ version to the original, and that multiple originals not produce the same hashed output. As with standard cryptography (in which unencrypted text is passed through an algorithm to generate encrypted text, and vice versa), the standard of ‘impossibility’ is really one of impracticability, given available computing resources and the sensitivity of the data in question. The hashed ‘fingerprint’ can be compared with a file and, if they still correspond, the integrity of the file is affirmed. Also, computer systems that store hashed versions of passwords do not pose the risk of yielding all user passwords in plain text form, if the files containing them are accidentally exposed of maliciously infiltrated. When users enter passwords to be authenticated, they can be hashed and compared with the stored version, without the need to store the unencrypted form. Given the frequency of ‘insider’ attacks within organizations, such precautions benefit both the users and owners of the systems in question.
Given their wide range of uses, the integrity of hash functions has become important for many industries and applications. For instance, they are used to verify the integrity of software security updates distributed automatically over the Internet. If malicious users were able to modify a file in a way that did not change the ‘fingerprint,’ as verified through a common algorithm, it could open the door to various kinds of attack. Alternatively, malicious users who could work backward from hashed data to the original form could compromise systems in other ways. They could, for instance, gain access to the unencrypted form of all the passwords in a large database. Since most people use the same password for several applications, such an attack could lead to further breaches. The SHA-1 algorithm, which has been widely used since 1995, was significantly compromised in February 2005. This was achieved by a team led by Xiaoyun Wang and primarily based at China’s Shandong University. In the past, the team had demonstrated attacks against MD5 and SHA: hash functions prior to SHA-1. Their success has prompted calls for a more durable replacement.
The need for such a replacement has now led the U.S. National Institute of Standards and Technology to initiate a contest to devise a successor. The competition is to begin in the fall of 2008, and continue until 2011. Contests like the one ongoing have a promising history in cryptography. Notably, the Advanced Encryption Standard, which was devised as a more secure replacement to the prior Data Encryption Standard, was decided upon by means of an open competition between fifteen teams of cryptographers between 1997 and 2000. At least some of those disappointed in that contest are now hard at work on what they hope will become one of the standard hash functions of the future.
Ten days to chapter two
By the end of this month, I am to submit the second chapter of my thesis. On “problem identification and investigation” it will detail the scientific processes that led to the Stockholm Convention and the Kyoto Protocol. Largely because of the sheer scale of the latter effort, it is a more difficult thing to pin down, especially in a reasonably concise way. If someone knows of an article or chapter that provides a neat scientific history of the climate change debate, UNFCCC, and Kyoto, I would appreciate being pointed in that direction.
On the theoretical side, the chapter will examine the ways in which phenomena in the world are categorized as ‘problems’ or not. I am also going to examine the role of existing bureaucratic structures in determining if and how scientific research in undertaken. There, the contrast between the American and Canadian approaches to dealing with POPs should be illustrative.
About 7,000 words long, this chapter will be one of the three pillars upon which the thesis as a whole will succeed or fail. As such, I am understandably anxious to do as good a job on it as can be managed, given the limitations on how much I can actually read and remember. My biggest source of anxiety remains the thought that I haven’t done enough research to speak authoritatively on the subject. Finishing the Litfin and Bernstein books is thus the first order of business, for the next few days. To that end, I should resume my ‘peripatetic and caffeinated’ reading strategy.
Richard Casement internship
As one more project for the next couple of weeks, I am going to prepare a submission for the Richard Casement internship at The Economist. Since about ten people a day are finding my site by searching for that term, I am not going to give any hints about what I might write my 600 word article about. That said, I am told that such applications generally succeed through the combination of a good submission with a fortuitous personal connection with someone already inside the organization. Furthermore, their stated “aim is more to discover writing talent in a science student or scientist than scientific aptitude in a budding journalist” and I am neither of those things.
That said, I can hardly imagine a better way to spend the first three months after finishing here than writing about science in New York or London. Hopefully, my application this year will go better than the ones I submitted in past recruiting cycles.
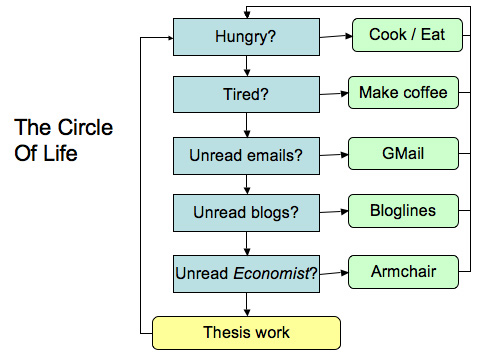
Alternative thesis flowchart
Introduction draft (v0.3) complete
Through the liberal application of Red Bull and Beethoven, a 4,802 word draft of my thesis introduction is ready to be dropped off tomorrow for my supervisor to read. I’ll give it one more read-over before printing it in the morning.
With seventy-seven days to go until submission, here is the state of the project:
Introduction: 4,802 words (5,477 with footnotes)
Chapter 2 – Problem identification and investigation: 2,753 words
Chapter 3 – Consensus formation in science and politics: 0 words
Chapter 4 – Remedy design and implementation 0 words
Conclusion: 0 wordsTotal: 7555 (25%)
Note: there are significant sections that were written in the old structure and have not found homes in the new structure yet. Most of them will land in Chapters 3 and 4.
My next chapter is due on February 28th. Just having the a draft introduction written makes me feel much more as though I am on top of this project, though parts of it will certainly need to be revised once the three substantive chapters have been written.
Tomorrow, I should also finish Kuhn and move on to Bernstein and Litfin. I also need to work out which bits of Haas need to be read most urgently.
[Update: 5 February 2007] I am starting to look forward to April, when the task will be to cut what I have written down to the correct length. (v0.4) of the introduction, which I just submitted, crept up to 5,018 words (5,894 with footnotes).
Thesis typeface: three options
While it may seem trivial to some, I do think it is worthwhile to put some effort into the selection of the font in which my thesis will be written and ultimately printed. For reasons of aesthetics and ease of reading, a fairly classical serif font is the sort being considered. Within that genre, there are three options I am considering most strongly at the moment.
Marshaling paragraphs
Sorry to go on and on about the thesis, but for some reason it has been dominated my attention recently. It has now taken on the character of being much like those large maps of Europe on which officers push around little tanks with long wooden poles. The tanks are there, the terrain is there, but their positions with respect to one another keep changing. A section on the nature of environmental ‘problems’ is somewhere near the border between the introduction and the first substantive chapter. Other bits have yet to be deployed into the theatre of operations, despite being fairly well constituted in and of themselves. Others are like the fledgling brigades of the new Iraqi army: assembled, in some sense, but far from ready to operate as part of a larger operation.
The draft introduction being submitted tomorrow is best seen as a first attempt to deploy a coherent strategy, with plenty of bits to be filled out later. The central issue is working out a broad way by which to coordinate the operations of disparate units, so as to develop sensible (if not entirely comprehensive) coverage of the terrain in dispute.
[Update: 8:30pm] This evolving draft section from my thesis may also be of use to general readers of this blog: Appendix I: Glossary and Table of Acronyms For those times when you can’t keep remember what was happening when UNECE (part of ECOSOC) negotiated the CLRTAP to deal with POPs (including PCBs).